Octelium
A next-gen FOSS self-hosted unified zero trust secure access platform that can operate as a remote access VPN, a ZTNA platform, API/AI/MCP gateway, a PaaS, an ngrok-alternative and a homelab infrastructure.
Install / Use
/learn @octelium/OcteliumQuality Score
Category
Development & EngineeringSupported Platforms
README
Table of Contents
- What is Octelium?
- Use Cases
- Main Features
- Try Octelium in a Codespace
- Install CLI Tools
- Install your First Cluster
- Useful Links
- License
- Support
- Frequently Asked Questions
- Legal
What is Octelium?
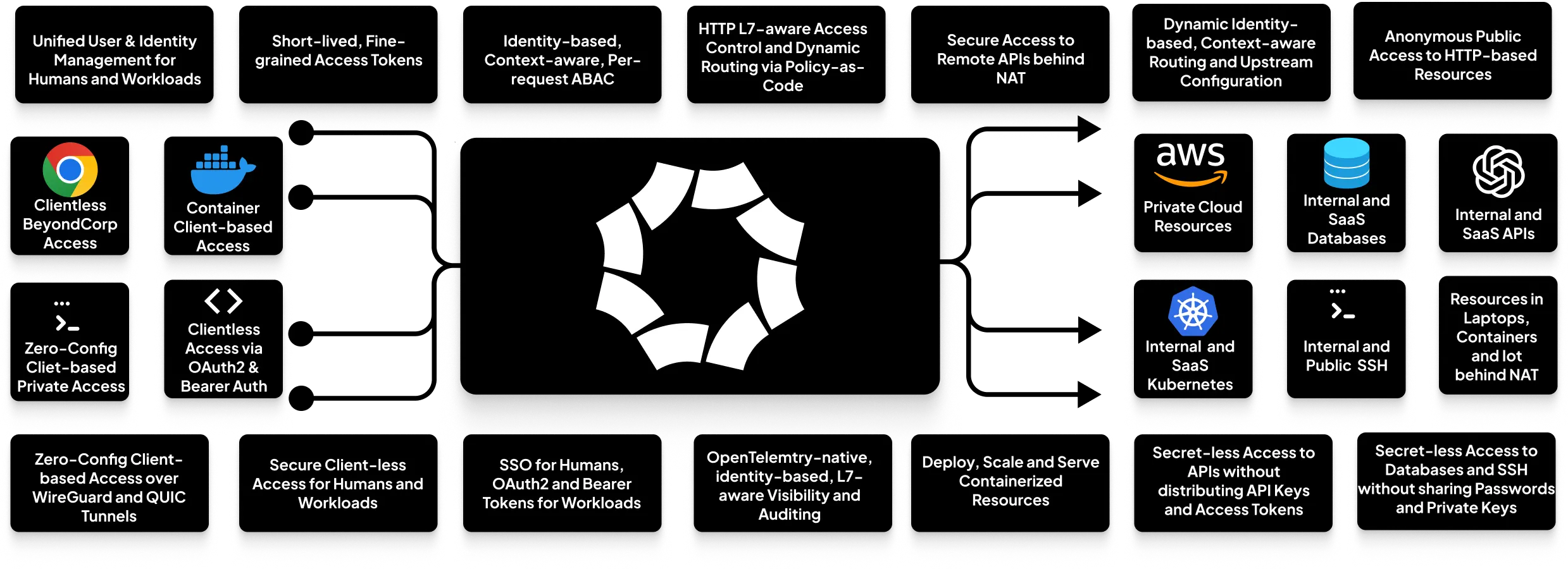
Octelium is a free and open source, self-hosted, unified zero trust secure access platform that is flexible enough to operate as a modern zero-config remote access VPN, a comprehensive Zero Trust Network Access (ZTNA)/BeyondCorp platform, an ngrok/Cloudflare Tunnel alternative, an API gateway, an AI/LLM gateway, a scalable infrastructure for access and deployment to build MCP gateways and AI agent-based architectures/agentic meshes, a PaaS-like deployment platform for containerized applications, a Kubernetes gateway/ingress and even as a homelab infrastructure.
Octelium provides a scalable zero trust architecture (ZTA) for identity-based, application-layer (L7) aware secretless secure access via both private client-based access over WireGuard/QUIC tunnels as well as public clientless access, for both humans and workloads, to any private/internal resource behind NAT in any environment as well as to publicly protected resources such as SaaS APIs and databases, via context-aware access control on a per-request basis.
Use Cases
Octelium is a versatile platform that can serve as a complete or partial solution for many different needs. Here are some of the key use cases:
- Modern Remote Access VPN: A zero-trust, layer-7 aware alternative to commercial remote access/corporate VPNs like OpenVPN Access Server, Twingate, and Tailscale, providing both zero-config client access over WireGuard/QUIC and client-less access via dynamic, identity-based, context-aware Policies.
- Unified ZTNA/BeyondCorp Architecture: A comprehensive Zero Trust Network Access (ZTNA) platform, similar to Cloudflare Access, Google BeyondCorp, or Teleport.
- Self-Hosted Secure Tunnels: A programmable infrastructure for secure tunnels and reverse proxies for both secure identity-based as well as anonymous clientless access, offering a powerful, self-hosted alternative to ngrok or Cloudflare Tunnel. You can see an example here.
- Self-Hosted PaaS: A scalable platform to deploy, manage, and host your containerized applications, similar to Vercel or Netlify. See an example for Next.js/Vite apps.
- API Gateway: A self-hosted, scalable, and secure API gateway for microservices, providing a robust alternative to Kong Gateway or Apigee. You can see an example here.
- AI Gateway: A scalable AI gateway with identity-based access control, routing, and visibility for any AI LLM provider. See an example here.
- Unified Zero Trust Access to SaaS APIs: Provides secretless access to SaaS APIs for both teams and workloads, eliminating the need to manage and distribute long-lived and over-privileged API keys. See a generic example here, AWS Lambda here, and AWS S3 here.
- MCP Gateways and A2A-based Architectures A secure infrastructure for Model Context Protocol (MCP) gateways and Agent2Agent Protocol (A2A)-based architectures that provides identity management, authentication over standard OAuth2 client credentials and bearer authentication, secure remote access and deployment as well as identity-based, L7-aware access control via policy-as-code and visibility (see an example here).
- Homelab: A unified self-hosted Homelab infrastructure to connect and provide secure remote access to all your resources behind NAT from anywhere (e.g. all your devices including your laptop, IoT, cloud providers, Raspberry Pis, routers, etc...) as well as a secure deployment platform to deploy and privately as well as publicly host your websites, blogs, APIs or to remotely test heavy containers (e.g. LLM runtimes such as Ollama, databases such as ClickHouse and Elasticsearch, Pi-hole, etc...). See examples for remote VSCode, and Pi-hole.
- Kubernetes Ingress Alternative: A more advanced alternative to standard Kubernetes ingress controllers and load balancers, allowing you to route to any Kubernetes service via dynamic, L7-aware policy-as-code (see an example here).
Main Features
-
A Modern, Unified Zero Trust Architecture Built on a scalable architecture of identity-aware proxies to control access at the application layer (L7), Octelium unifies access for humans and workloads to both private and protected public resources. It supports both zero-config VPN-like client-based access over WireGuard/QUIC and client-less BeyondCorp access, all built on top of Kubernetes for automatic scalability (read in detail about how Octelium works here).
-
Dynamic Secretless Access Octelium's layer-7 awareness enables Users to seamlessly access resources protected by application-layer credentials without exposing, managing and distributing such secrets (read more here). This works for HTTP APIs without sharing API keys and access tokens, SSH servers with sharing passwords and private keys, Kubernetes clusters, PostgreSQL/MySQL databases as well as any L7 protocol protected by mTLS.
-
Modern, Dynamic, Fine-grained Access Control Octelium provides you a modern, centralized, scalable, fine-grained, dynamic, context-aware, layer-7 aware, attribute-based access control system (ABAC) on a per-request basis (read more here) with policy-as-code using CEL and OPA (Open Policy Agent). Octelium has no notion of an "admin" user, enforcing zero standing privileges by default.
-
Context-aware, identity-based, L7-aware dynamic configuration and routing Route to different upstreams, different credentials representing different upstream contexts and accounts using policy-as-code with CEL and OPA on a per-request basis. You can read in detail about dynamic configuration here.
-
Continuous Strong Authentication A unified authentication system for both human and workload Users, supporting any web identity provider (IdP) that uses OpenID Connect or SAML 2.0 as well as GitHub OAuth2 (read more here). It also allows for secretless authentication for workloads via OIDC-based assertions (read more here). Built-in support for MFA/re-authentication/login via FIDO2/WebAuthn/Passkey, TOTP and TPM 2.0 Authenticators.
-
OpenTelemetry-native Auditing and Visibility Real-time, identity-based, L7-aware visibility and access logging. Every request is logged and exported to your OpenTelemetry OTLP receivers for seamless integration with your log management and SIEM tools.
-
Effortless, Passwordless SSH Octelium clients can serve SSH even without root access, enabling you to SSH into containers, IoT devices, or other hosts that can't run an SSH server (read more here).
-
Effortlessly deploy, scale and secure access to your containerized applications as Services Octelium provides you out-of-the-box PaaS-like capabilities to effortlessly deploy, manage and scale your containerized applications and serve them as Services to provide seamless secure client-based private access, client-less public BeyondCorp access as well as public anonymous access. You can read in detail about managed containers here.




