BrowserBruter
BrowserBruter is a powerful web form fuzzing automation tool designed for web security professionals and penetration testers. This Python-based tool leverages Selenium and Selenium-Wire to automate web form fuzzing, making it easier to identify potential vulnerabilities in web applications.
Install / Use
/learn @netsquare/BrowserBruterREADME
The Browser-Bruter
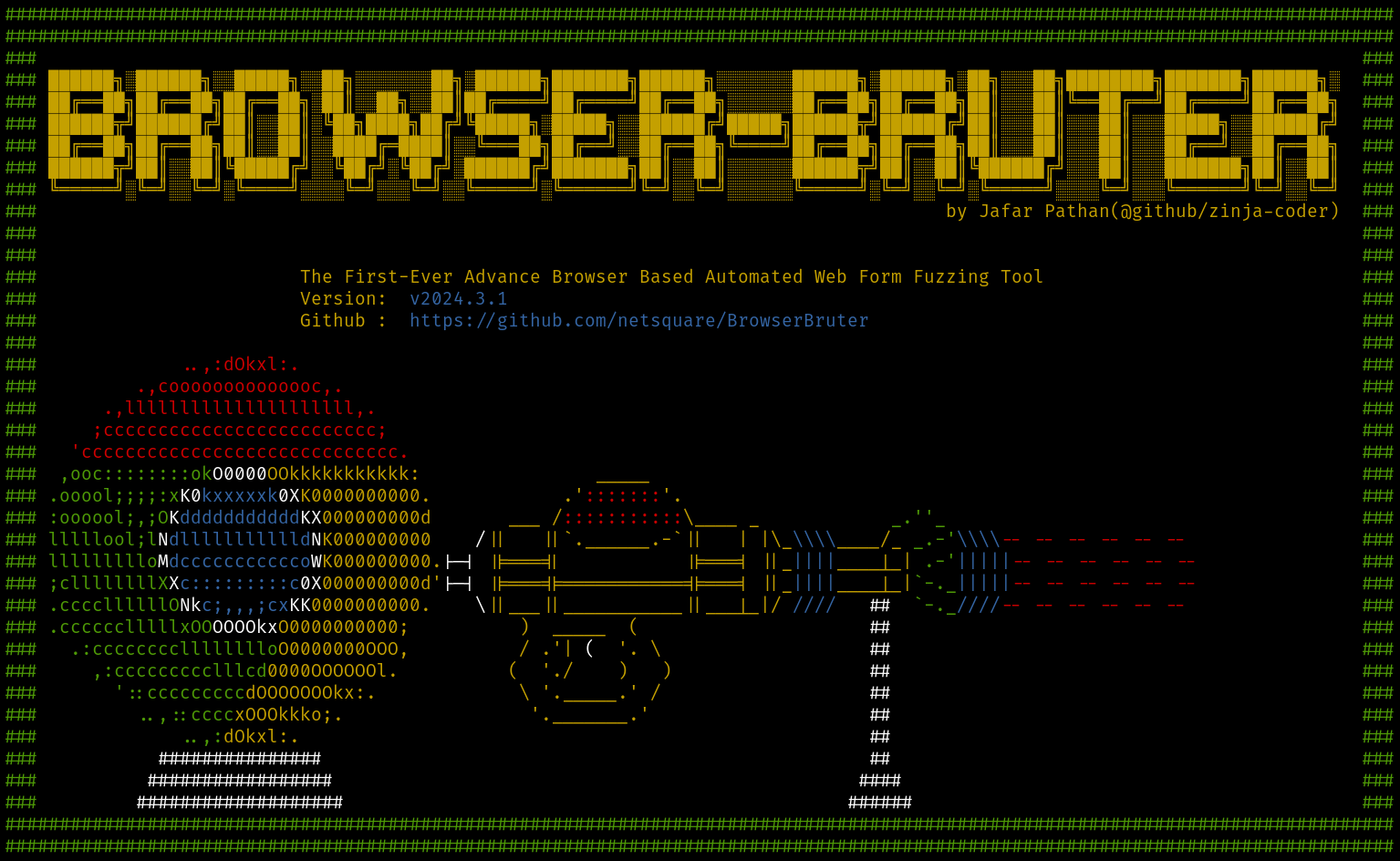
The Browser-Bruter is first ever browser based automated web pentesting tool for fuzzing web forms by controlling the browser it self. It automates the process of sending payloads to input fields of browser and sends them too server. It completely bypasses the need of breaking the encryption in order to fuzz and insert payloads in BurpSuite scanner and intruder. After fuzzing it generates a comprehensive report including all the data and result of the pentest along with HTTP traffic, this report can be viewed by The Report-Explorer tool which comes with The Browser-Bruter.
Handcrafted in India 🇮🇳
<img width="1024" height="1536" src="https://github.com/user-attachments/assets/cdb800c6-66e2-44aa-880c-c0d9abb93ee4" />Please refer to this for Proof of Concept of our claims - https://net-square.com/browserbruter/WhyWeNeedBrowserBruter/
Proof Of Concept
HTTP Manipulation ineffective due to Encryption
https://net-square.com/browserbruter/img/need-1.mp4
Trying to find SQLInjection using SQLMAP
https://net-square.com/browserbruter/img/sqlmap.mp4
Trying to find SQLInjection using BurpSuite
https://net-square.com/browserbruter/img/burp-scan.mp4
BruteForcing login page using FFUF
https://net-square.com/browserbruter/img/ffuf-1-video.mp4
Finding SQL Injection which can not be found in other tools using The Browser Bruter
https://net-square.com/browserbruter/img/sql-injection.mp4
BruteForcing Login page using The Browser Bruter
https://net-square.com/browserbruter/img/brute-force-login-1.mp4
Please refer official documentation for installation and to learn how to use, It is highly recommended. You can find the official documentation - https://net-square.com/browserbruter/
- Download now!
- Jump to Installation
- Jump to How to use
- Click here to know Why we created The BrowserBruter
Sample Demos:
Cracking The Captchas by Integrating ML into Browser Bruter:
https://github.com/user-attachments/assets/c30cda8b-29f3-442e-817d-5939325b01e2
Automatic Navigation Handler Module in action:
https://github.com/user-attachments/assets/a3be207c-a744-490b-865e-01974814fffc
Bypassing rate limit via custom Pyton Script:
https://github.com/user-attachments/assets/cc91636a-a792-41a5-aa0c-cf9f65a6800c
Integration with AI using MCP and crack encryption like never before:
What it does?
The biggest advantage of using browser bruter for fuzzing the web application is that all of the fuzzing will take place at browser level, so all of the attack will be as they have been manually done by the user by typing payloads in the input fields of the web application on browser.
This approach -
-
Allows Pentester to fuzz the web application forms when the HTTP body (or part of the body) is encrypted making HTTP proxy tools like ZAP and BurpSuite or SQLMap unable to insert payloads in such traffic. Learn more here.
-
Creates a way to bypass captchas by allowing the pentester to manually perform the required human interactions and then proceed to payload insertions.
-
Can fuzz front-end when there is no HTTP traffic, for example when Input is utilized on the client side, i.e. when you want to brute force OTP input which is validated on the client side, so there is no HTTP Traffic.
-
Removes the burden of session management, auth handling and other micro management like CSRF handling while using HTTP proxy tools.


Prerequisites
- Linux
- Python3
Quick Installation
Download and Run Using UV - 0 manual installation
-
Download from latest release
-
Install the
uvutility
curl -LsSf https://astral.sh/uv/install.sh | sh
### Then directly run
uv run BrowserBruter.py --help
OR manual way (not recommended)
- Download and install Python3
- Download the latest release from releases.
- Unzip the archive.
- Run
pip3 install -r requirements.txt - Done
Refer documentation for detailed installation guide. - https://net-square.com/browserbruter/SetupInstallation/
Setting up the MCP Server
🤖 Using Claude Desktop
Here we are demonstrating for claude desktop, but the server should work with every AI Agent/Client capable of MCP. For example, for LM Studio you have to configure the mcp.json file of LMStudio to add MCP Servers.
Make sure Claude Desktop is running with MCP enabled. Make sure you have uv utility installed.
For instance, I have used following for Kali Linux: https://github.com/aaddrick/claude-desktop-debian
Configure and add MCP server to LLM file:
nano ~/.config/Claude/claude_desktop_config.json
And following content in it:
{
"mcpServers": {
"Browser-Bruter-MCP-Server": {
"command": "/<path>/<to>/uv",
"args": [
"--directory",
"</PATH/TO/>/BrowserBruter/modules/mcp/",
"run",
"browser_bruter_mcp_server.py"
]
}
}
}
# For Example
{
"mcpServers": {
"Browser-Bruter-MCP-Server": {
"command": "/home/zinjacoder/.local/bin/uv",
"args": [
"--directory",
"/home/zinjacoder/softwares/tools/built/BrowserBruter/modules/mcp/",
"run",
"browser_bruter_mcp_server.py"
]
}
}
}
# To run as HTTP Stream based server
{
"mcpServers": {
"Browser-Bruter-MCP-Server": {
"command": "/path/to/uv",
"args": [
"--directory",
"path/to/BrowserBruter/modules/mcp/",
"run",
"browser_bruter_mcp_server.py --http --port <port(default is 8652)>"
]
}
}
}
Replace:
path/to/uvwith the actual path to your uv executablepath/to/BrowserBruter/modules/mcp/with the absolute path to where you downloaded the BrowserBruter
Then run below command to start BrowserBruter in MCP mode:
python3 BrowserBruter.py --mcp --target https://example.com
### You will see
INFO: MCP data handler running at http://localhost:9011
After this, start you AI Agent (Claude Desktop/ LMStudio) and send prompts to crack the encryption.
<img width="512" height="316" alt="image" src="https://github.com/user-attachments/assets/892a68ac-57fa-4a03-81d8-94ff4dd9d93b" />And you can also build the command to run Browser Bruter using AI as shown in video below:
https://github.com/user-attachments/assets/8f96ab59-8ab2-4d5a-8b4c-d25c5120615f
Current MCP Tools:
- get_current_url - Fetch the current browser URL and page title.
- get_dom_snapshot - Get the current DOM snapshot. In other words, get the current web page's source code.
- get_browser_bruter_switches_and_arguments - Fetch the available switches and arguments in BrowserBruter to know it's functionality and build a cli command.
- get_screenshot - Fetch the screenshot of the currently opened web page in browser.
- analyze_page_forms - Analyze all forms on the current page and extract detailed information about inputs, buttons, and validation mechanisms.
- fetch_encryption_logic - Detect and fetch the client-side encryption logic of HTTP traffic.
- analyze_specific_function - Fetch and analyze specific function.
- detect_validation_mechanisms - Detect client-side validation mechanisms that might interfere with fuzzing attempts.
- suggest_payloads_for_inputs - Analyze input fields and suggest appropriate payloads based on field types and names.
Current MCP Prompts:
- Build Browser Bruter Command
- Build Browser Bruter Command using dom snapshot
Test Lab for BrowserBruter
The Lab shown in documentation can be setup using docker as follows-
- Download and run the docker image -
sudo docker run --rm -p 80:80 hpandro/vims - Start the MySQL service using following -
- First copy the container id using
sudo docker container ls -a - Then start the service using
sudo docker exec -it [containerid] service mysql startNavigate tohttp://localhost/to test site.
- First copy the container id using
Working Flow Overview
Features
- Bypass Encryption
- Multiple Attack Modes 1. Sniper 2. Battering Ram 3. PitchFork 4. Cluster Bomb
- [Guaranteed Report Generation even in crash](https://net-square.com/browserbruter/U







