Fanny.bmp
fanny.bmp cleaned MALWARE - ONLY FOR ACADEMICAL RESEARCH AND EDUCATIONAL PURPOSES! (incl Metasploit detection Module)
Install / Use
/learn @loneicewolf/Fanny.bmpREADME
⚠️ MALWARE AHEAD! — RESEARCH ONLY ⚠️
If you don’t know what this is, stop here.
This repository contains malware samples and research materials for academic, reverse engineering, and forensics purposes only.
Do NOT run anything outside of isolated environments (e.g., air-gapped VMs).
Fanny.BMP / DementiaWheel Overview
- Related to
Brutal_Kangaroo - Connected to
nls_933w.dll - Infects via USB using CVE-2010-2568
- Shares DNA with Stuxnet and Flame, gauss and duqu respectievely
- modules LNK 1 RAPID7 fanny_bmp_check - By Me
- vulnerabilities LNK 2 RAPID7 fanny_bmp_check - By Me
- metasploit-framework LNK 3 SRC of fanny_bmp_check - By Me
Rootkit Demonstration
shelldoc.dll GUI Stealth Sample:
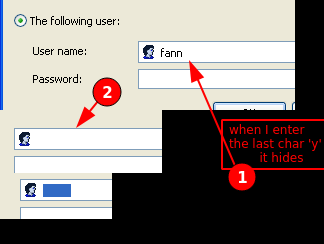
✔️ Demonstrates that the rootkit hides
.lnkand keyword-matching files even from system UI dialogs. Which demonstrates it's not just a simple file hider, it's a generalized rootkit that hides dirs(verify this claim)/files[x]/even strings[x]
Technical Report
A full report was written, but will be rewritten soon for clarity and accuracy. The update will focus on:
- Technical deep dives
- Relationship to Equation Group tools
- Ethical simulation techniques
🗂️ Project Contributions
Fanny detection added to:
🧪 Basic Malware Info
<details> <summary>Click to expand</summary>Name: Fanny.BMP (aka DementiaWheel)
Type: USB-propagating Worm
Exploits: CVE-2010-2568 (LNK exploit)
Targets: Windows XP → Windows 10
Payloads: Explorer rootkit, USB storage exfiltration, persistence via ACM driver
CVE: CVE-2010-2568
Reference: https://securelist.com/a-fanny-equation-i-am-your-father-stuxnet/68787/
POCs & Hashes
<details> <summary>Click to expand full list of samples + VirusTotal links</summary>Includes:
- All
__*.lnkUSB autoloaders comhost.dll,mscorwin.dll,shelldoc.dll,ECELP4.ACM,agentcpd.dll- Primary dropper (
fanny.bmp) - Temporary file (
~DE1923.tmp)
Example:
</details>Metasploit Integration
You can detect Fanny infections using the
fanny_bmp_checkmodule in Metasploit:
meterpreter > run post/windows/gather/forensics/fanny_bmp_check
Expected output:
[+] HKEY_LOCAL_MACHINE\SYSTEM\...\ECELP4\Driver found
[+] HKEY_LOCAL_MACHINE\SYSTEM\...\ECELP4\filter2 found
...
POC Videos
Reproduction Bugs & Notes
Creating
.lnkfiles named__e__.lnkunder XP withshelldoc.dllactive may crash Explorer.✔️ This has been captured and documented in video + screenshots.
Future Plans
- Improved USB C2 bridge w/ Metasploit
- C+Lua tooling for USB backdoor command & control
- Fully structured academic writeup
- Screenshots and annotated source
Related Research
Why Release This?
To help defenders, researchers, and detection engineers. These files are hard to find. Collecting + analyzing them helps strengthen infosec.
References
MALWARE AHEAD
Branch of interest:
Acknowledgements
Thanks to
- Fyyre - for your DrvMon
- Hfiref0x - for your KDU
- GPT(O3-PRO) For helping me check the formulation of this repo, like MarkDown, etc.
- FSU's 2 Students Alejandro Ugas and McDougall for their Research
Security Score
Audited on Mar 30, 2026
