WireTapper
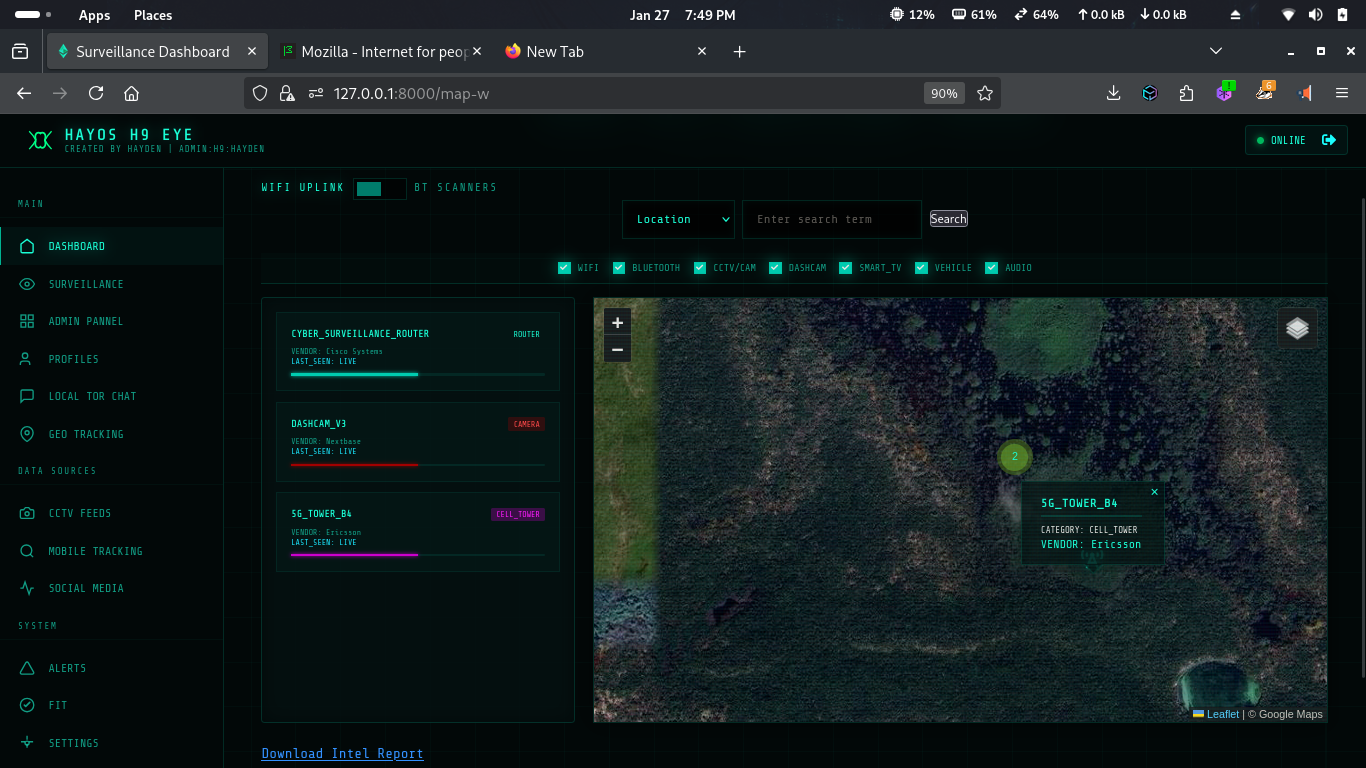
WireTapper is a wireless OSINT tool that passively detects and maps Wi-Fi, Bluetooth, CCTV cameras, vehicles, headphones, TVs, IoT devices, and cell towers, turning nearby radio signals into clear situational intelligence 📡
Install / Use
/learn @h9zdev/WireTapperREADME
📡 WireTapper
<p align="center"> <img src="https://raw.githubusercontent.com/h9zdev/WireTapper/main/images/WireTapper.png" alt="WireTapper" /> </p>[!NOTE] Wireless OSINT & Signal Intelligence Platform
WireTapper is a wireless OSINT tool designed to discover, map, and analyze radio-based devices using passive signal intelligence. It provides investigators, researchers, and security analysts with real-time visibility into the invisible wireless landscape around them.
WireTapper detects and correlates signals from common wireless technologies, helping users understand what devices exist, where they are likely located, and how they interact, without active intrusion.
WireTapper identifies leaked Wi-Fi network credentials based on privacy-protecting k-Anonymity query scheme.
<p align="center"> 🔗 <strong>Website:</strong> <a href="https://haybnz.web.app?utm_source=github.com">https://haybnz.web.app</a> </p> <p align="center"> 🔗 <strong>Blog on WireTapper:</strong> <a href="https://medium.com/@h9z/wire-tapper-wireless-osint-signal-intelligence-platform-e5104659a1cb?utm_source=github.com"> Read on Medium </a> </p> <p align="center"> <a href="https://github.com/sponsors/h9zdev"> <img src="https://img.shields.io/badge/Make%20a%20Difference-Sponser%20My%20Work-6A1B9A?style=for-the-badge&logo=github&logoColor=white" alt="Support My Work" /> </a> </p> <p align="center"> <a href="https://github.com/h9zdev/WireTapper"> <img src="https://img.shields.io/static/v1?label=Python&message=WireTapper&color=2A3E87&labelColor=6A7DA8&style=for-the-badge&logo=python&logoColor=white" /> </a> <a href="https://github.com/h9zdev/WireTapper/issues"> <img src="https://img.shields.io/github/issues/h9zdev/WireTapper?style=for-the-badge&color=8B0000&logo=github" /> </a> <a href="https://github.com/h9zdev/WireTapper/network/members"> <img src="https://img.shields.io/github/forks/h9zdev/WireTapper?style=for-the-badge&color=455A64&logo=github" /> </a> <a href="https://github.com/h9zdev/WireTapper/stargazers"> <img src="https://img.shields.io/github/stars/h9zdev/WireTapper?style=for-the-badge&color=FFD700&logo=github" /> </a> </p>📶 Supported Signal Intelligence
WireTapper can identify and analyze signals from:
- Wi-Fi access points & clients, Wi-Fi credentials leak
- Bluetooth & BLE devices
- Wireless CCTV / IP cameras
- Vehicles broadcasting RF signals (infotainment, telemetry, keyless systems)
- Headphones, wearables, and smart devices
- Smart TVs & IoT appliances
- Cell towers & mobile network beacons
🔑 API Services
WireTapper integrates with several external services to provide intelligence. You will need to obtain API keys from the following:
- Wigle.net – Wireless network mapping and discovery.
- wpa-sec – Distributed WPA-PSK auditor database.
- OpenCellID – Open-source database of cell towers.
- Shodan – Search engine for Internet-connected devices.
- Note: A Premium account is required to use Shodan's API with this tool.
🚀 Installation
Follow these steps to get WireTapper up and running:
-
Clone the repository:
git clone https://github.com/h9zdev/WireTapper.git cd WireTapper -
Install dependencies: It is recommended to use a virtual environment.
pip install -r WireTapper.txt -
Configure API Keys and Run:
Choose one of the following methods to configure your API keys and run the application:
Method 1: Modify
app.py(Direct Configuration)Open
app.pyand manually enter your API keys by replacing the empty strings:WIGLE_API_NAME = "your_wigle_api_name" WIGLE_API_TOKEN = "your_wigle_api_token" OPENCELLID_API_KEY = "your_opencellid_api_key" SHODAN_API_KEY = "your_shodan_api_key"Then, start the server:
python app.pyMethod 2: Use
app-env.py(Environment Variables)This is the recommended approach for better security. You can export your keys in the terminal:
export WIGLE_API_NAME="your_wigle_api_name" export WIGLE_API_TOKEN="your_wigle_api_token" export OPENCELLID_API_KEY="your_opencellid_api_key" export SHODAN_API_KEY="your_shodan_api_key"Alternatively, you can define these keys in a
.envfile. Then, start the server:python app-env.pyThe application will be available at
http://localhost:8080/map-w.
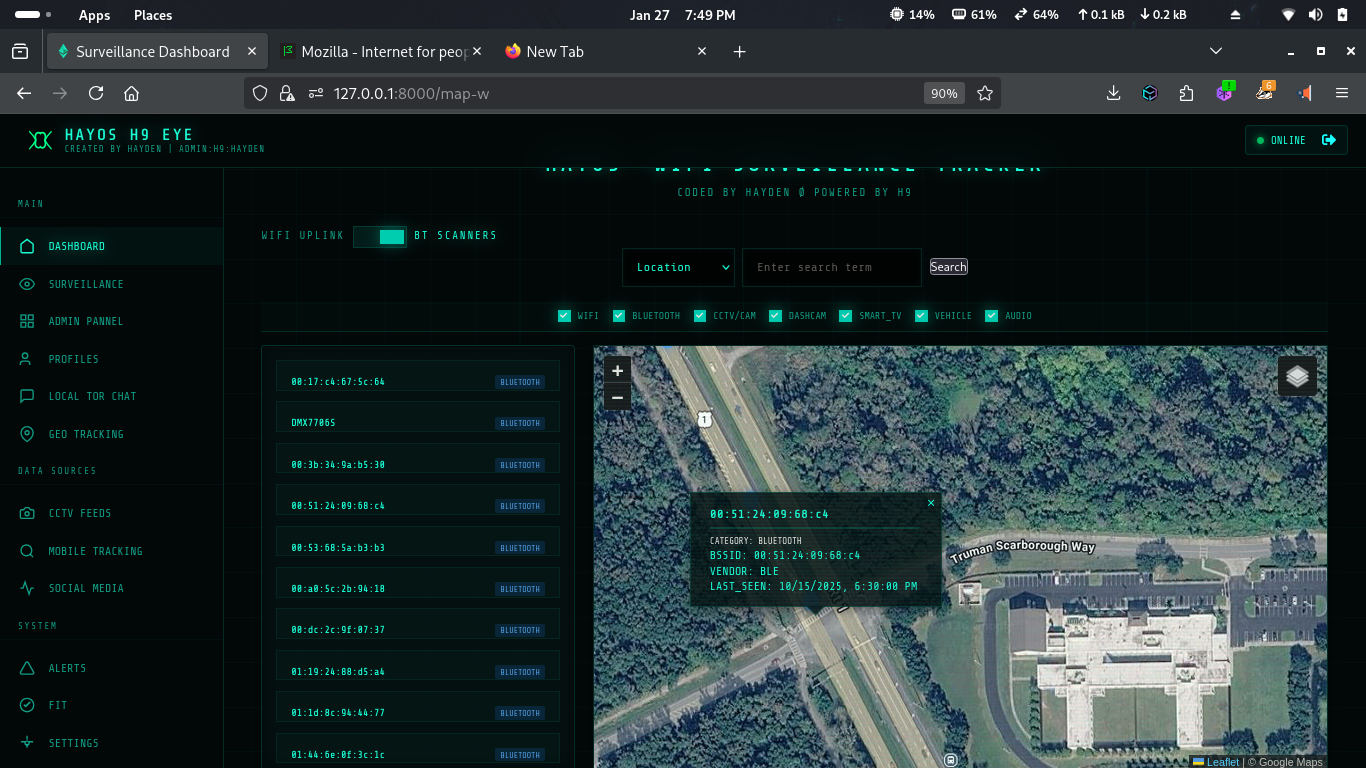
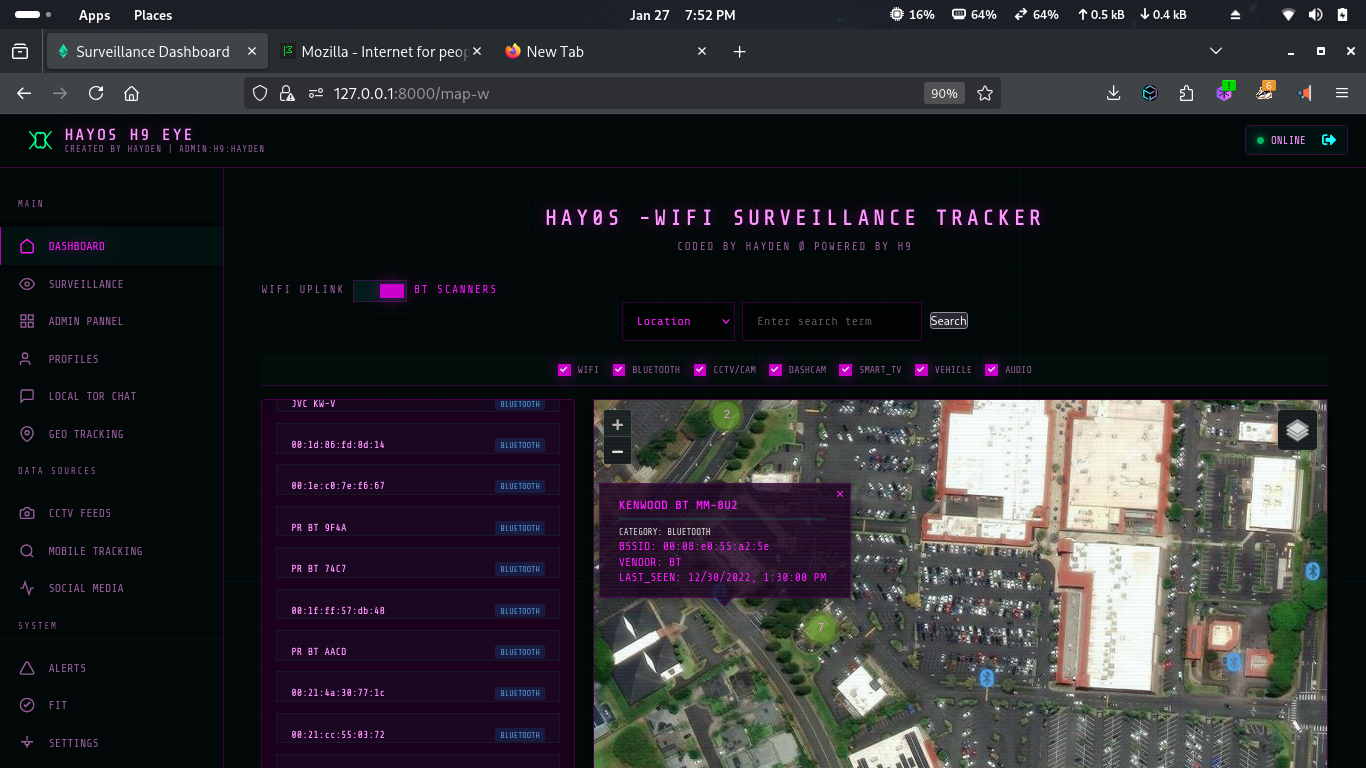
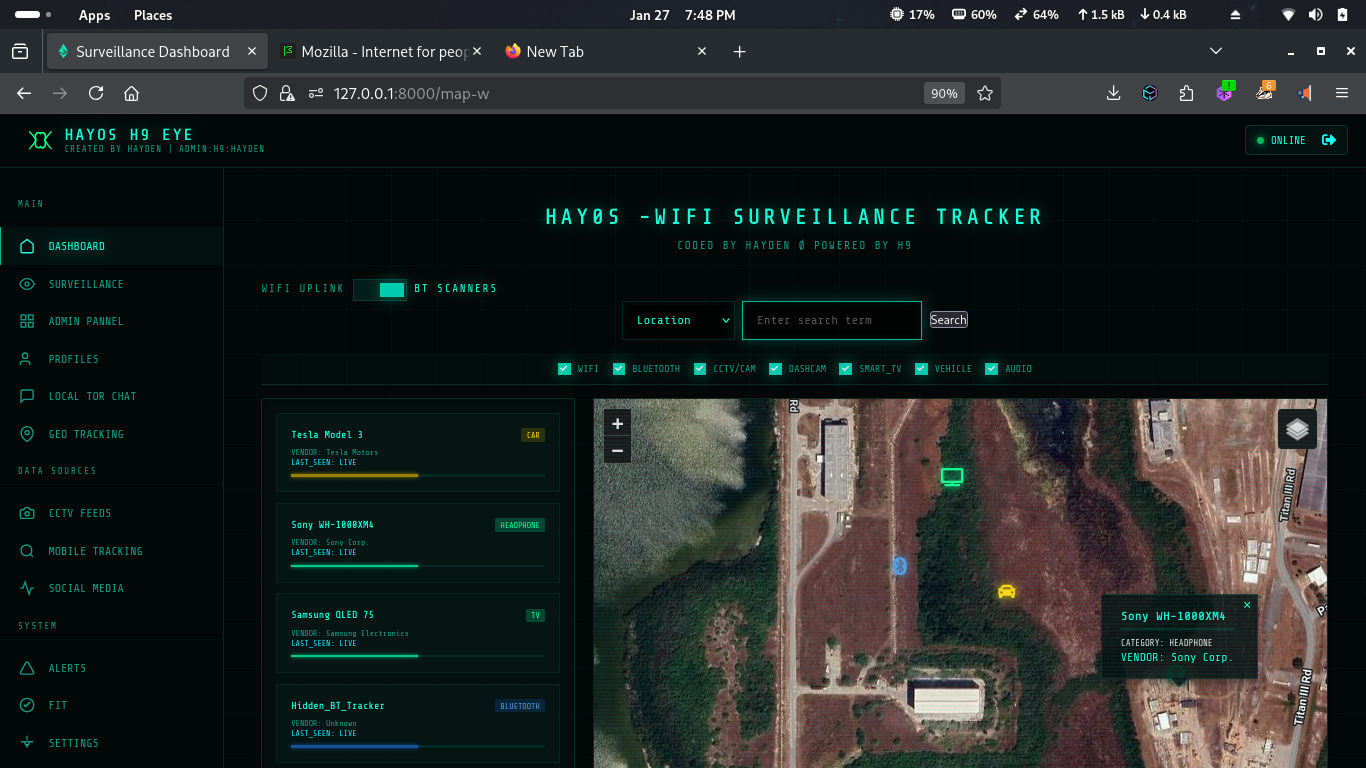
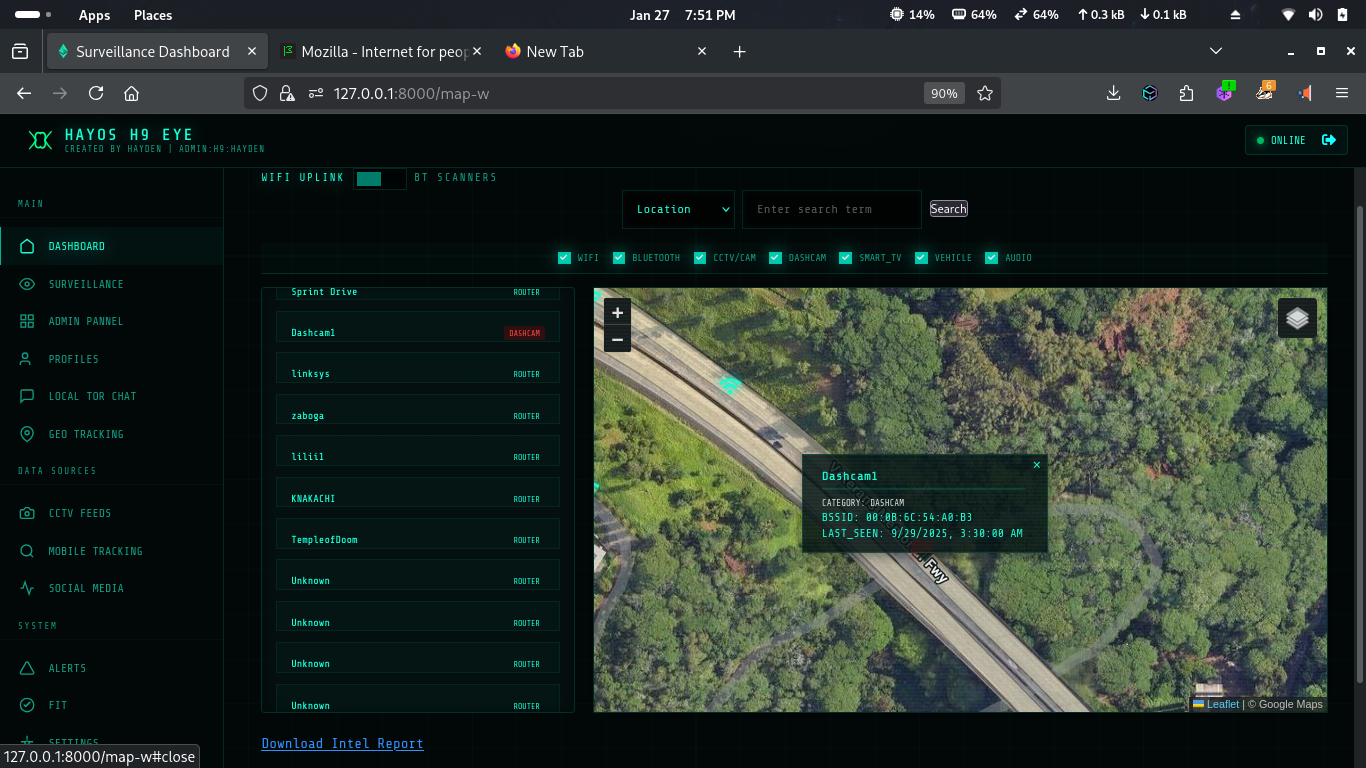
📷 Screenshots
📜 License
This project is licensed under the Creative Commons Attribution-NonCommercial 4.0 International (CC BY-NC 4.0) License. See the LICENSE file for more details.
Unauthorized use is strictly prohibited.
📧 Contact: singularat@protn.me
☕ Support
Donate via Monero: 45PU6txuLxtFFcVP95qT2xXdg7eZzPsqFfbtZp5HTjLbPquDAugBKNSh1bJ76qmAWNGMBCKk4R1UCYqXxYwYfP2wTggZNhq
👥 Contributors and Developers
<img src="https://avatars.githubusercontent.com/u/67865621?s=64&v=4" width="64" height="64" alt="haybnzz"> <img src="https://avatars.githubusercontent.com/u/108749445?s=64&v=4" width="64" height="64" alt="VaradScript">
