Jsbro
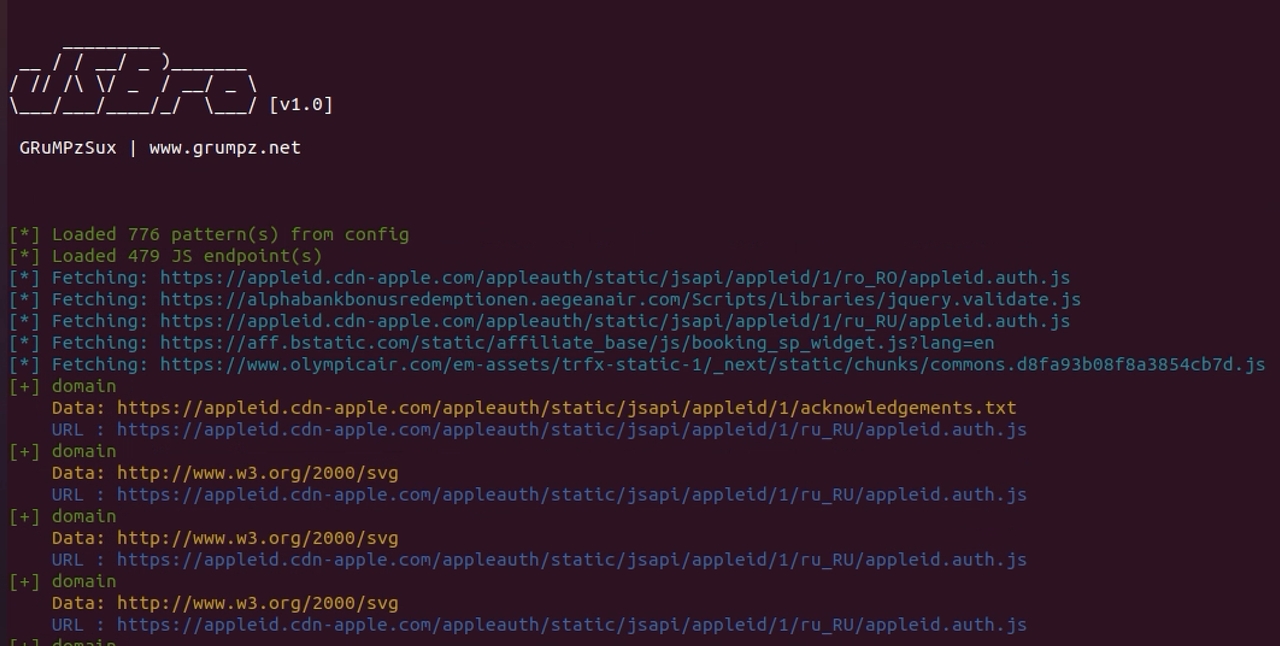
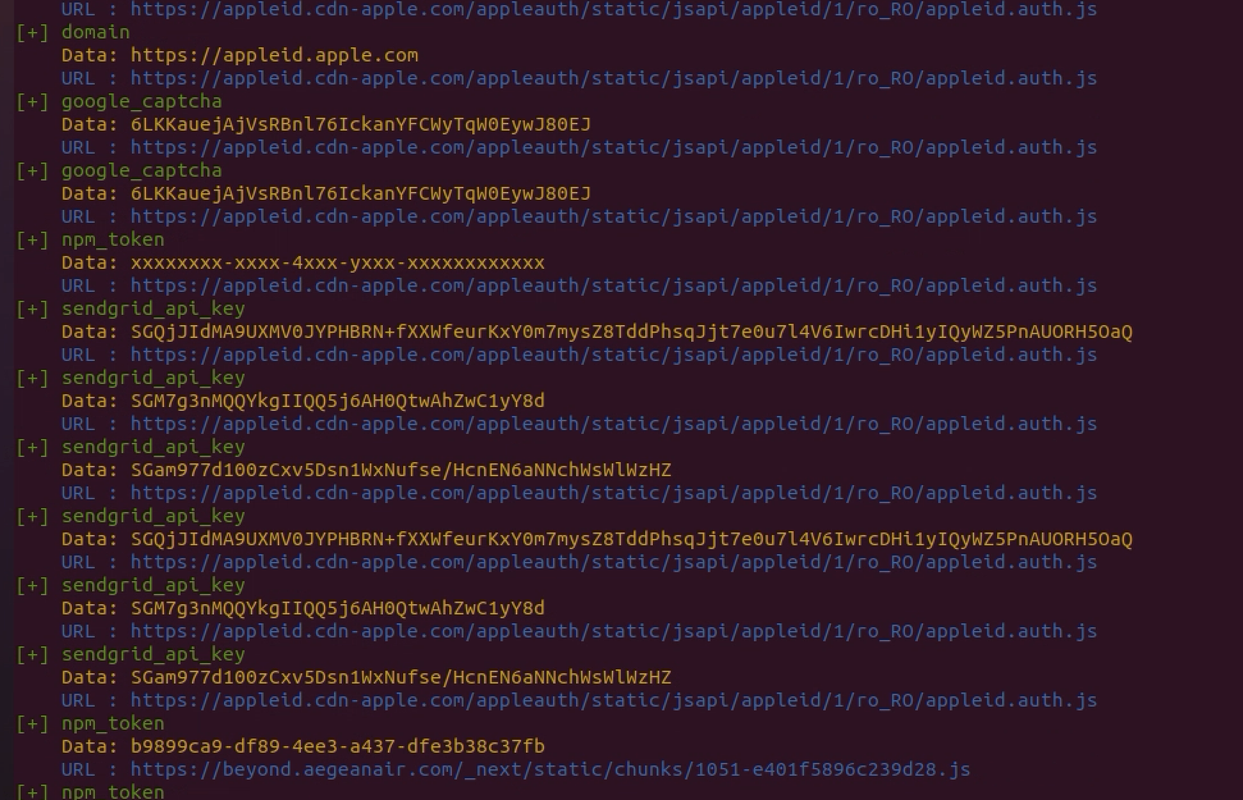
A simple yet powerful tool for scanning multiple JavaScript endpoints for leaks and secrets using regex patterns.
Install / Use
/learn @grumpzsux/JsbroREADME
JSBro
JSBro is a powerful and fast tool written in Go for scanning JavaScript endpoints for secrets and sensitive information. By leveraging user-defined regex patterns (via YAML configuration), JSBro helps you quickly identify potential security leaks across a list of JavaScript URLs.
Features
- Concurrent Processing: Scan multiple JS endpoints at once with configurable concurrency.
- Customizable Regex Patterns: Easily define and update regex patterns using a YAML configuration file.
- Colorful, User-Friendly Output: Results are clearly presented in your terminal with color coding for easy identification.
Installation
Make sure you have Go installed (version 1.16+ recommended).
You can install JSBro directly using the go install command:
go install -v github.com/grumpzsux/jsbro@latest
This will compile JSBro and install the binary into your $GOPATH/bin.
Alternatively, clone the repository and build it manually:
git clone https://github.com/grumpzsux/jsbro.git
cd jsbro
go build -o jsbro main.go
Usage
JSBro requires two inputs:
- A endpoint list file (
--listor-l) that contains one JavaScript endpoint URL per line. - A YAML configuration file (
--configor-c) that defines the regex patterns to search for, check the/patterns/directory. - A concurrency speed, the default is set to 5 (
--concurrencyor-n) that defines how fast you want to scan.
Example command:
./jsbro --list /path/to/endpoints.txt --config /path/to/patterns.yaml --concurrency 10
If you would like to save the output to a text file, simply tee the output:
jsbro -list URL-list.txt -c patterns/leakin-regexes.yml -n 10 | tee jsLeaked.txt
Example YAML Configuration
Below is an example of a YAML configuration file:
patterns:
- pattern:
name: AWS Access Key
regex: "(A3T[A-Z0-9]|AKIA|AGPA|AIDA|AROA|AIPA|ANPA|ANVA|ASIA)[A-Z0-9]{16}"
confidence: high
- pattern:
name: AWS Secret Key
regex: "(?i)aws(.{0,20})?(?-i)['\\\"][0-9a-zA-Z\\/+]{40}['\\\"]"
confidence: high
Contributing
Contributions are welcome! Please fork the repository and submit your pull requests. If you find any issues or have suggestions, feel free to open an issue on GitHub.
Contact
For questions or support, send me a Direct Message on X @GRuMPzSux
Related Skills
node-connect
351.4kDiagnose OpenClaw node connection and pairing failures for Android, iOS, and macOS companion apps
frontend-design
110.7kCreate distinctive, production-grade frontend interfaces with high design quality. Use this skill when the user asks to build web components, pages, or applications. Generates creative, polished code that avoids generic AI aesthetics.
openai-whisper-api
351.4kTranscribe audio via OpenAI Audio Transcriptions API (Whisper).
qqbot-media
351.4kQQBot 富媒体收发能力。使用 <qqmedia> 标签,系统根据文件扩展名自动识别类型(图片/语音/视频/文件)。
