Defguard
Zero-Trust access management with true WireGuard® 2FA/MFA
Install / Use
/learn @DefGuard/DefguardREADME
Website | Getting Started | Features | Roadmap | Support ❤
</div>Open, transparent, verifiable and inspectable
- Our security approach: https://defguard.net/security/
- Our public penetration tests reports: https://defguard.net/pentesting/
- Daily SBOM CVE scan: https://defguard.net/sbom/
- Our detailed roadmap: https://github.com/orgs/DefGuard/projects/5
- Our Architecture Decision Records: https://app.gitbook.com/o/Z3mGSAbEj9iLdZ7cNFlL/s/kHPDOBrb5X1TB8O3GsjW/~/changes/86/in-depth/architecture-decision-records
Defguard provides Comprehensive Access Control (a complete security platform):
- WireGuard® VPN with 2FA/MFA - not 2FA to "access application" like most solutions
- The only solution with automatic and real-time synchronization for users' desktop client settings (including all VPNs/locations).
- Control users ability to manage devices and VPN options
- ACLs/Firewall Management for Linux and FreeBSD/OPNSense
- Integrated SSO based on OpenID Connect:
- significant cost saving, simplifying deployment and maintenance
- enabling features unavailable to VPN platforms relying upon 3rd party SSO integration
- Already using Google/Microsoft or other OpenID Provider? - external OpenID provider support
- Two way Active Directory/LDAP synchronization
- Only solution with secure remote user Enrollment & Onboarding
- Yubico YubiKey Hardware security key management and provisioning
- Secure and robust architecture, featuring components and micro-services seamlessly deployable in diverse network setups (eg. utilizing network segments like Demilitarized Zones, Intranet with no external access, etc), ensuring a secure environment.
- Enterprise ready (multiple Locations/Gateways/Kubernetes deployment, etc..)
- Built on WireGuard® protocol which is faster than IPSec, and significantly faster than OpenVPN
- Built with Rust for speed and security
See:
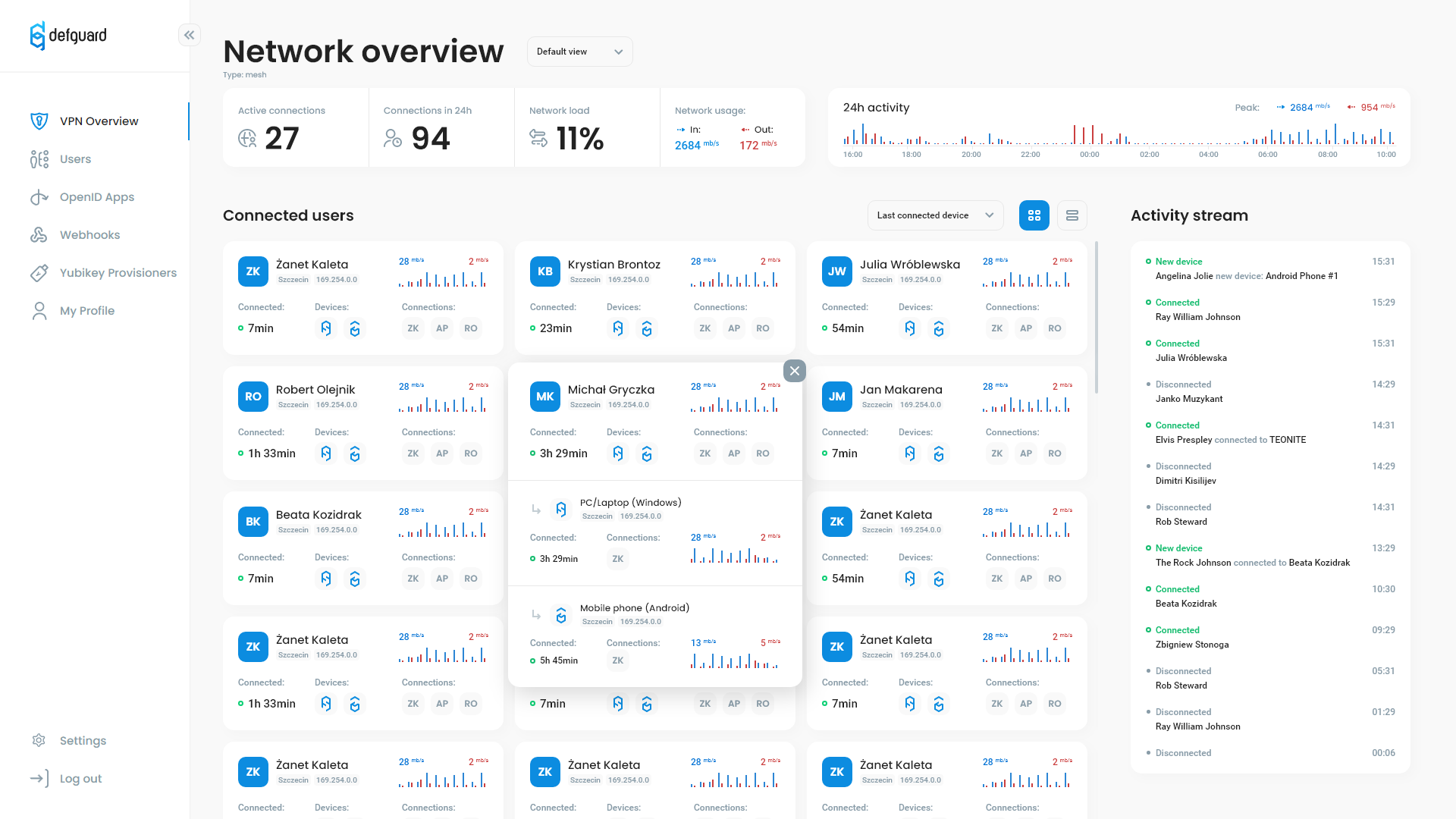
Defguard makes it easy to manage complex VPN networks in a secure way
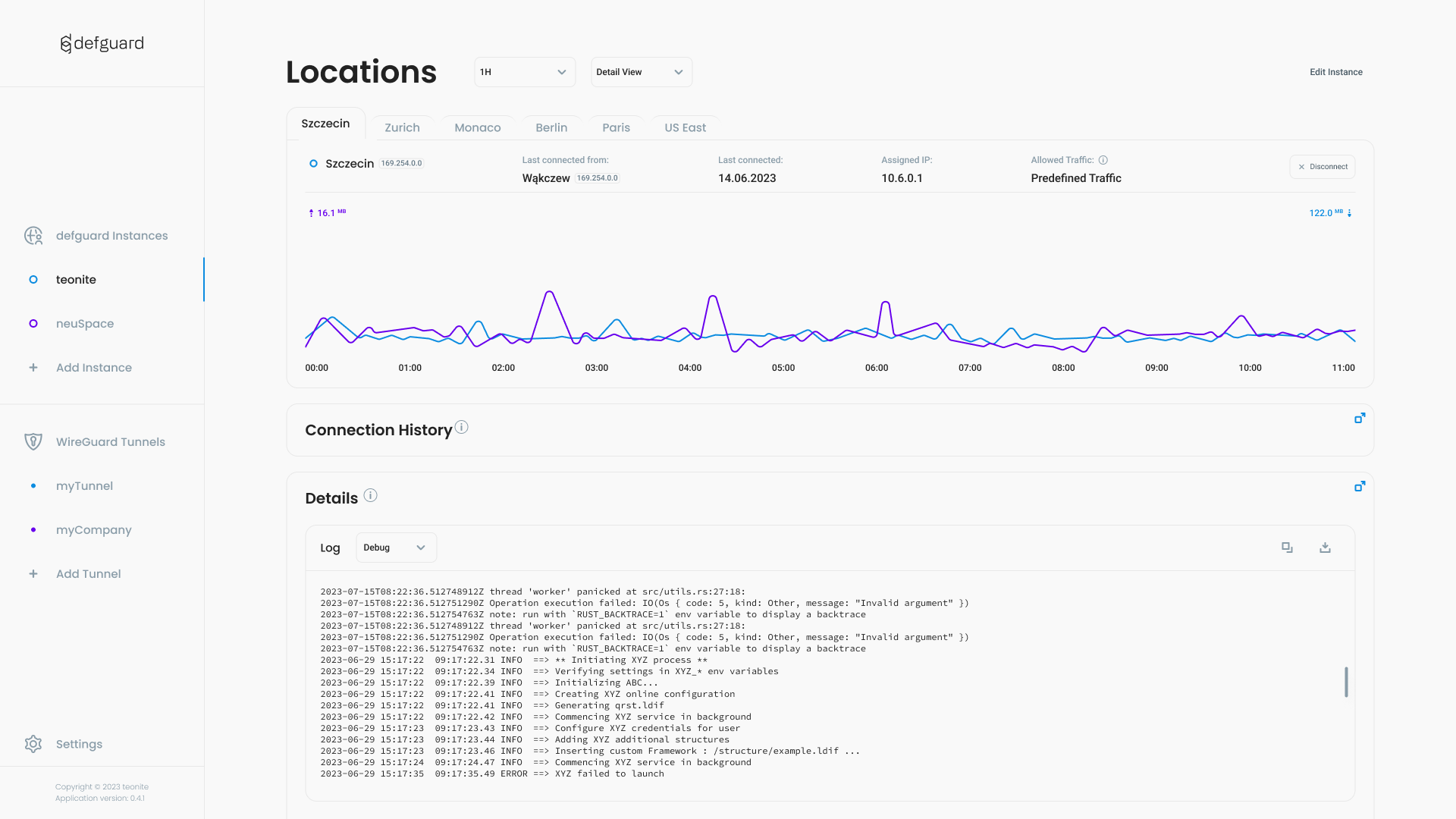
<img width="1564" alt="locations-connections" src="https://github.com/user-attachments/assets/f886750b-1d4e-467e-917d-bc19a86e275c" />Video introduction
Bear in in mind we are no youtubers - just engineers - here is a video introduction to defguard:
<div align="center"> <p align="center"> </p> </div>Control plane management (this video is few versions behind... - a lot has changed!)

Better quality video can be viewed here
Desktop Client with 2FA / MFA (Multi-Factor Authentication)
Light
Dark

- 2FA / Multi-Factor Authentication with TOTP or email based tokens & WireGuard PSK
- automatic and real-time synchronization for users' desktop client settings (including all VPNs/locations).
- Control users ability to manage devices and VPN options
- Defguard instances as well as any WireGuard tunnel - just import your tunnels - one client for all WireGuard connections
- Secure and remote user enrollment - setting up password, automatically configuring the client for all VPN Locations/Networks
- Onboarding - displaying custom onboarding messages, with templates, links ...
- Ability to route predefined VPN traffic or all traffic (server needs to have NAT configured - in gateway example)
- Live & real-time network charts
- live VPN logs
- light/dark theme
Quick start
The easiest way to run your own defguard instance is to use Docker and our one-line install script. Just run the command below in your shell and follow the prompts:
curl --proto '=https' --tlsv1.2 -sSf -L https://raw.githubusercontent.com/DefGuard/deployment/main/docker-compose/setup.sh -O && bash setup.sh
Here is a step-by-step video about this process:
<div align="center"> <p align="center"> </p> </div>To learn more about the script and available options please see the documentation.
Setup a VPN server in under 5 minutes !?
Just follow this tutorial
Manual deployment examples
Roadmap & Development backlog
A detailed product roadmap and development status can be found here
⛑️ Want to help? ⛑️
Here is a dedicated view for good first bugs
Features
- Remote Access: WireGuard® VPN server with:
- Multi-Factor Authentication with TOTP/Email & Pre-Shared Session Keys
- multiple VPN Locations (networks/sites) - with defined access (all users or only Admin group)
- multiple Gateways for each VPN Location (high availability/failover) - supported on a cluster of routers/firewalls for Linux, FreeBSD/PFSense/OPNSense
- import your current WireGuard® server configuration (with a wizard!)
- most beautiful Desktop Client! (in our opinion ;-))
- automatic IP allocation
- automatic and real-time synchronization for users' desktop client settings (including all VPNs/locations).
- control users ability to manage devices and VPN options
- kernel (Linux, FreeBSD/OPNSense/PFSense) & userspace WireGuard® support with our Rust library
- dashboard and statistics overview of connected users/devices for admins
- defguard is not an official WireGuard® project, and WireGuard is a registered trademark of Jason A. Donenfeld.
- Identity & Account Management:
- SSO based on OpenID Connect](https://openid.net/developers/how-connect-works/)
- External SSO: external OpenID provider support
- Multi-Factor/2FA Authentication:
- Time-based One-Time Password Algorithm (TOTP - e.g. Google Authenticator)
- WebAuthn / FIDO2 - for hardware key authentication support (eg. YubiKey, FaceID, TouchID, ...)
- Email based TOTP
- LDAP (tested on OpenLDAP) synchronization
- forward auth for reverse proxies (tested with Traefik and Caddy)
- nice UI to manage users
- Users self-service (besides typical data management, users can revoke access to granted apps, MFA, WireGuard®, etc.)
- Account Lifecycle Management:
- Secure remote (over the Internet) user enrollment - on public web / Desktop Client
- User onboarding after enrollment
- SSH & GPG public key management in user profile - with SSH keys authentication for servers
- [Yubikey hardware k
Related Skills
healthcheck
334.5kHost security hardening and risk-tolerance configuration for OpenClaw deployments
node-connect
334.5kDiagnose OpenClaw node connection and pairing failures for Android, iOS, and macOS companion apps
prose
334.5kOpenProse VM skill pack. Activate on any `prose` command, .prose files, or OpenProse mentions; orchestrates multi-agent workflows.
frontend-design
82.2kCreate distinctive, production-grade frontend interfaces with high design quality. Use this skill when the user asks to build web components, pages, or applications. Generates creative, polished code that avoids generic AI aesthetics.


